How to Use Microsoft Copilot Effectively at Work. A Practical Guide for Smarter, Safer AI Use

The Practical Guide to Microsoft Copilot for Business | John Grennan Business & Technology • AI Insights The Practical Guide to Microsoft Copilot for Business Practical tips, smarter prompting techniques, and real‑world examples to get more value from Microsoft 365 Copilot. JG John Grennan Published on April 16, 2026 Microsoft Copilot is not just a […]
If You Wouldn’t Post It on Social Media, Don’t Paste It Into AI

If You Wouldn’t Post It on Social Media, Don’t Paste It Into AI | it.ie AI Data Privacy & Security If You Wouldn’t Post It on Social Media, Don’t Paste It Into AI JG John Grennan • 12/02/2026 AI tools like ChatGPT, Gemini and others have quickly become the modern office assistant. They summarise emails, […]
Domain Registration Scam Warning

Domain Registration Scam Warning 2026 | Fake Renewal Invoices Author: John Grennan | Published: January 22, 2026 Security Alert Domain Registration Scam Warning. Fake Renewal Invoices Are Back Domain registration scams are not new. But they are getting more polished, more convincing, and more likely to catch busy businesses off guard. We were recently sent […]
5 New Year’s IT Resolutions Every Irish SME Should Make

📅 Looking Ahead to 2026 5 New Year’s IT Resolutions Every Irish SME Should Make A new year. The same IT risks if nothing changes. 2026 is shaping up to be a defining year for how Irish businesses approach security and growth. January is when many businesses set goals around growth and efficiency. IT rarely […]
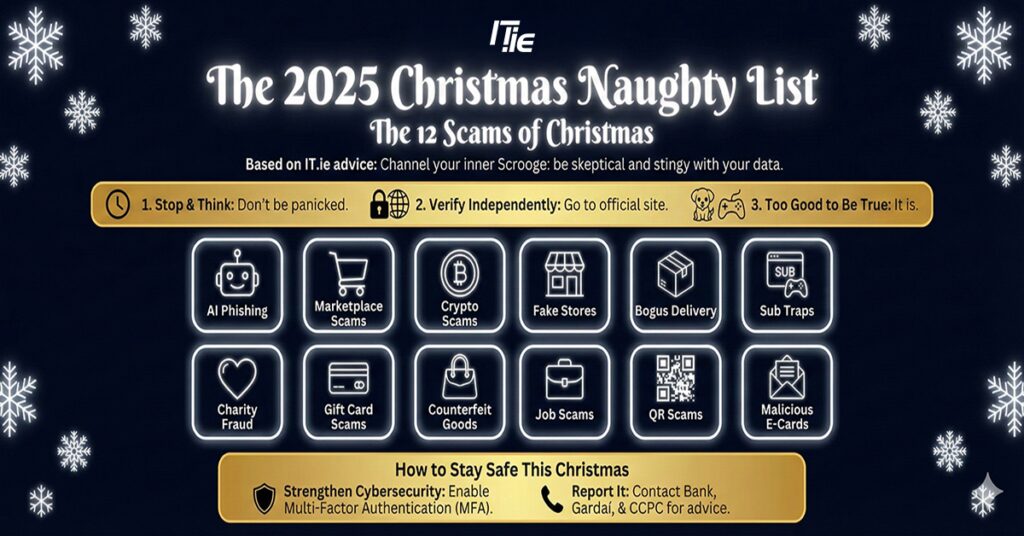
The 2025 Christmas Naughty List
Ireland’s Year in Search 2025

Ireland’s Year in Search 2025 Right then, time to put the kettle on and settle down, because we have cracked open the data for Ireland’s Google Year in Search 2025. This annual deep dive gives us a brilliant, often baffling, look at what exactly has been occupying the minds (and phone screens) of the Irish […]
Cyber Security Myths vs Reality: What Irish SMEs Need to Know
Cyber Security Myths vs Reality: What Irish SMEs Need to Know Our news feeds are constantly scrolling with stories of major brands falling victim to cyber-attacks. It is easy to look at those headlines and think, “Well, at least I’m not them.” However, that mindset is dangerous. Many Irish businesses are operating under a set […]
The Privacy Paradox with AI
Artificial intelligence (AI) is rapidly transforming how we work, communicate, and make decisions but concerns around data privacy have never been more pressing. The rapid rise of AI assistants such as Microsoft Copilot, OpenAI’s ChatGPT, and Google Gemini has brought powerful capabilities to our fingertips but at what cost to our personal and organisational data? […]
Press Release: 30% of office workers have tried to gain unauthorised access to a colleague’s device in the last year

Research from IT.ie and SonicWall also found that 35% have actively sought out private information about a colleague, client, or customer from a work computer system 38% have engaged with a scammer either intentionally or unintentionally One in four have sent an angry response to someone they presumed to be a scammer 17% say they […]
In-House vs Managed IT Services – What’s Right for Your Business?
As your business grows, so too do your IT needs. Maybe you have someone on the team who’s ‘good with computers’, or you’ve been relying on a one-person IT setup. At some point, you’ll face a decision: Do we build an in-house IT team, or partner with a Managed IT Services provider? This post will […]

