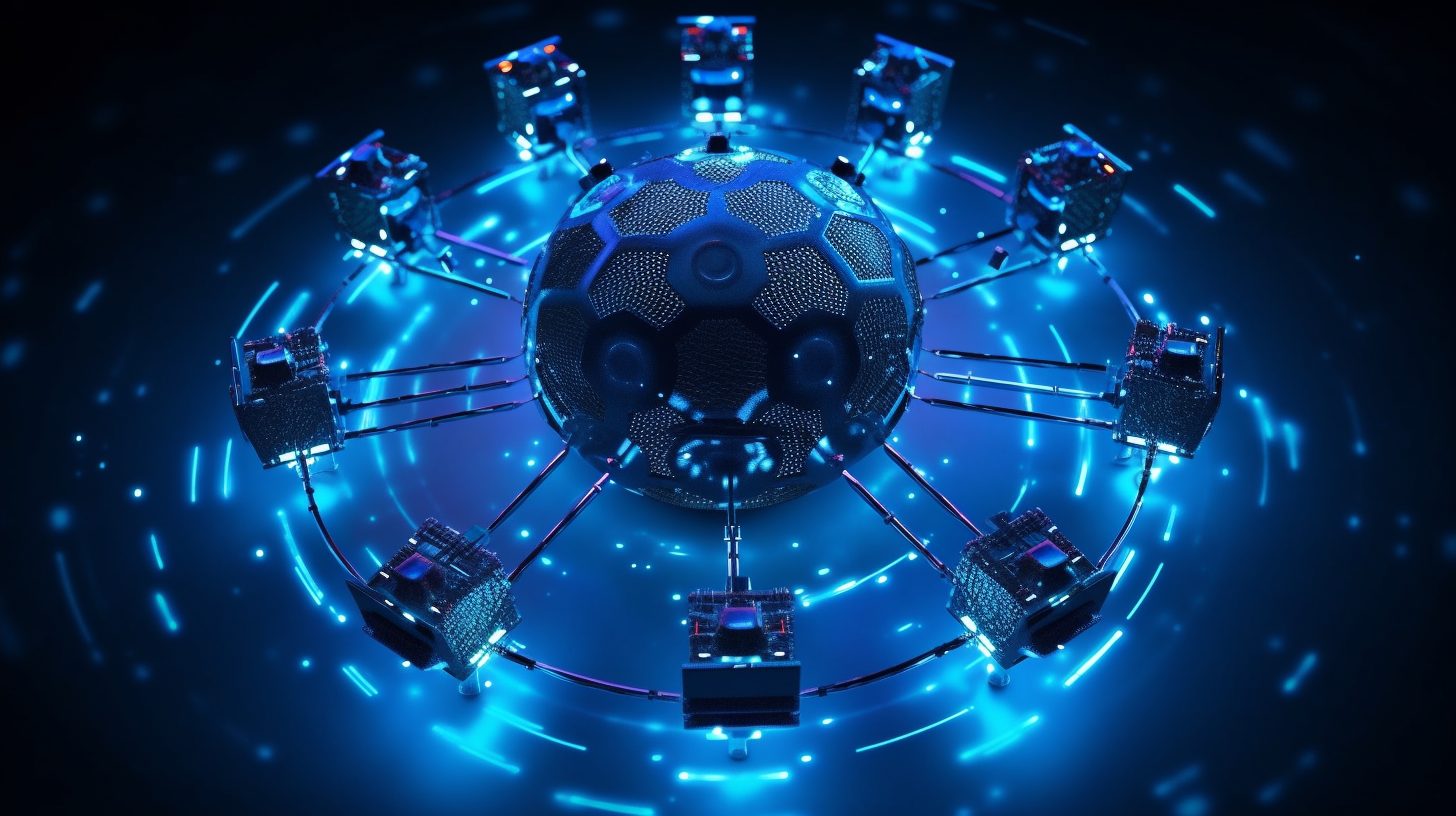
Zero Trust Security is a revolutionary cybersecurity model that challenges traditional perimeter-based security practices. Unlike traditional approaches that assume trust within the network, Zero Trust operates under the principle of “never trust, always verify.” It emphasises continuous verification of every user, device, and application attempting to access resources, regardless of their location.
In the past, organisations relied on a castle-and-moat approach to security, with a strong perimeter defense protecting the internal network. However, with the rise of cloud services, mobile devices, and remote work, the traditional network perimeter has become porous, leaving organisations vulnerable to sophisticated cyber threats. Zero Trust Security addresses this challenge by implementing a comprehensive security framework that provides granular access controls and continuous monitoring.
At its core, Zero Trust Security shifts the focus from network-centric security to a more user-centric and data-centric approach. It assumes that no user or device, whether inside or outside the network, is automatically trusted. Instead, it treats every access request as potentially malicious and requires strong authentication and verification for each attempt to access resources.
Zero Trust Security emphasizes continuous verification of user identity, device health, and application integrity. Users and devices are authenticated and authorized at every access request, ensuring only legitimate entities gain access to sensitive resources.
Zero Trust Security promotes the segmentation of networks and resources into smaller, isolated segments. This approach limits the lateral movement of threats, preventing them from easily propagating across the network.
Zero Trust Security takes into account contextual information such as user location, device health, and network conditions to dynamically adapt access controls. This ensures that access privileges are tailored to the specific situation and can be adjusted in real-time as conditions change.
Zero Trust follows the principle of least privilege, granting users the minimum access privileges necessary to perform their tasks. This approach minimizes the potential damage that can be caused by compromised accounts or insider threats.
Zero Trust Security relies on continuous monitoring and analysis of user behavior, network traffic, and application interactions. This allows for real-time threat detection, anomaly detection, and prompt response to potential security incidents.
Authentication plays a crucial role in Zero Trust. Implementing multi-factor authentication adds an extra layer of security by requiring users to provide multiple credentials or factors to verify their identity. This approach significantly reduces the risk of unauthorized access, even if one factor (e.g., password) is compromised.


By adopting the Zero Trust Security model, organisations can establish a robust cybersecurity posture that protects against both internal and external threats. It helps mitigate the risk of data breaches, unauthorised access, and lateral movement within the network. Zero Trust Security is particularly effective in today’s dynamic and distributed IT environments, where traditional perimeter defenses are no longer sufficient.
At IT.ie, we specialise in helping organisations implement and optimise Zero Trust Security frameworks tailored to their specific needs. Our team of cybersecurity experts works closely with you to assess your security requirements, design a comprehensive Zero Trust strategy, and deploy the necessary technologies and controls. By partnering with us, you can strengthen your cybersecurity defenses, gain better visibility and control, and safeguard your valuable digital assets.

If you would like to talk to us or just have a question about any of our services, please don’t hesitate to contact us and we’ll get right back to you.
We and our partners use cookies and process personal data (like unique IDs and Browse behaviour) to improve your experience, personalize content and ads, measure performance, and understand our audience.
You have the right to choose which cookies you'd like to enable. By clicking "Accept", you consent to all cookies. You can also "Reject" non-essential cookies, or manage your preferences through "View Preferences" below.
For more information on how we use cookies and your data, please read our Cookie Policy and Privacy Policy.
Fill in your details below and hit download.